This issue is mainly present if you are trying to migrate from Exchange on-prem to Exchange Online and you’re not going with the hybrid route. The “double mailbox” way consists in having an online mailbox and a local one, and manually (or automatically using tools) migrating the content online.
The issue is that, if you are synchronizing your on-prem AD with Azure AD, you are most probably including your msExchMailboxGUID into the replicated fields. This attribute will tell Exchange Online not to create an online mailbox, as an on-prem one already exists.
Once you will have cleared this field from the online user, Exchange Online will be able to create another mailbox, populating the msExchMailboxGuid of the online user, leaving you with the possibility of exporting and importing data into your online mailbox.
Please note that this will also automatically clear the following attributes from the online user:
- alias
- legacyExchangeDN
- msExchArchiveGuid
- msExchArchiveName
- msExchBlockedSendersHash
- msExchElcMailboxFlags
- msExchRecipientDisplayType
- msExchRecipientTypeDetails
- msExchSafeRecipientsHash
- msExchSafeSendersHash
- userCertificate
To proceed with the creation of the online mailbox, follow these steps:
- Open your AD Connect server.
- Stop the Sync with Powershell (launch it as admin and keep it open after this command): Set-ADSyncScheduler -SyncCycleEnabled $false
- Open the Synchronization Rules Editor as an admin.

- Select the In from AD – User Exchange rule, click Edit, then click on yes.

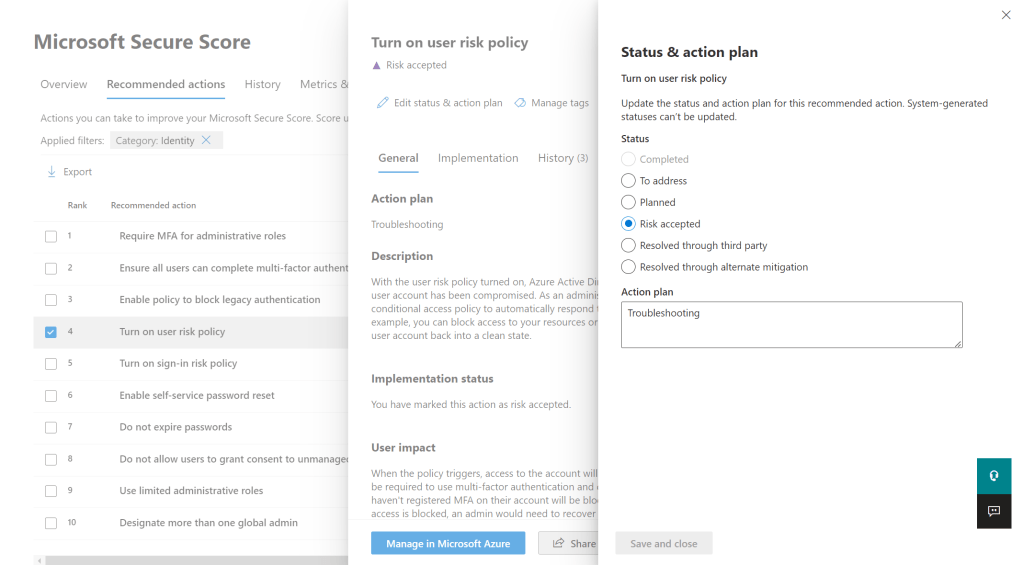
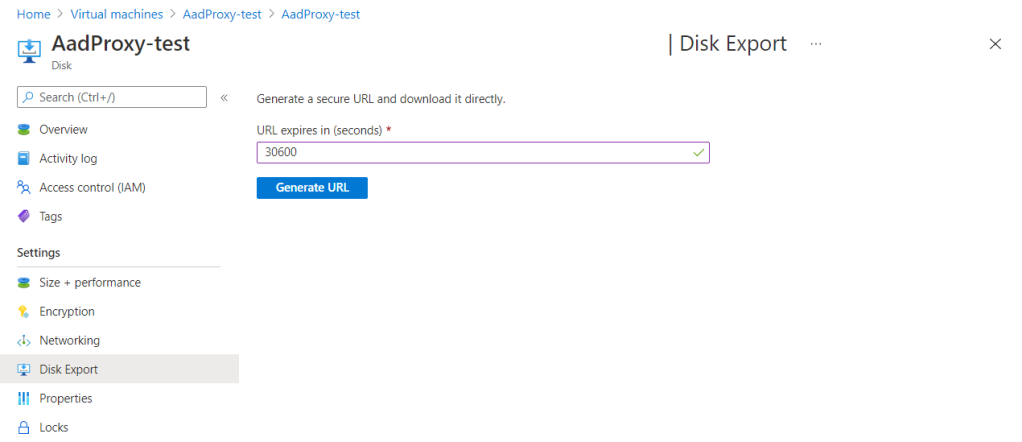
- Under Precedence write 250 (or the first free one), then click Next until you arrive in the Transformations page. Here look for msExchMailboxGuid, then change the row’s settings to make them match with the image below:

- Once you are done, click Save, then open the original rule. Note down the Precedence (usually it’s 108), then delete the rule. Go into your newly cloned rule and change the Precedence to the one you noted down.
- Before you enable the scheduler and perform a full sync, you should test out the changes. This is the documentation link to test everything out without committing changes to Azure AD: Verify changes to AD Connect rules | MS Docs
- Reenable the scheduler: Set-ADSyncScheduler -SyncCycleEnabled $true
- Perform a full synchronization: Start-ADSyncSyncCycle -PolicyType Initial
You should now be able to create a second mailbox for your synchronized user by assigning a valid license.